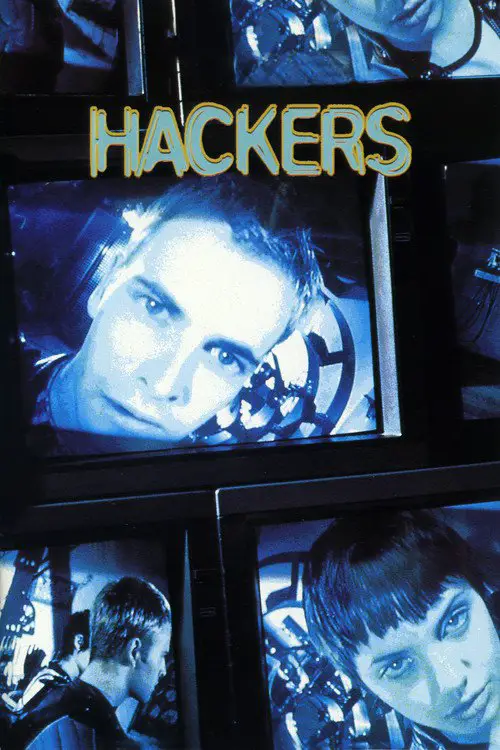
Hackers (1995)
Similar movies
Angela Bennett is a freelance software engineer who lives in a world of computer technology. When a cyber friend asks Bennett to debug a CD-ROM game, she discovers a conspiracy that will turn her life upside down. Soon, her records have been erased, and she's been given a new identity and a police record. Her vacation is ruined as she struggles to determine why she's been deleted from society.
When shadowy U.S. intelligence agents blackmail a reformed computer hacker and his eccentric team of security experts into stealing a code-breaking "black box" from a Soviet-funded genius, they uncover a bigger conspiracy. Now, he and his "sneakers" must save themselves and the world economy by retrieving the box back from their blackmailers.
Rogue agent Gabriel Shear is determined to get his mitts on $9 billion stashed in a secret Drug Enforcement Administration account. He wants the cash to fight terrorism, but lacks the computer skills necessary to hack into the government mainframe. Enter Stanley Jobson, a n'er-do-well encryption expert who can log into anything.
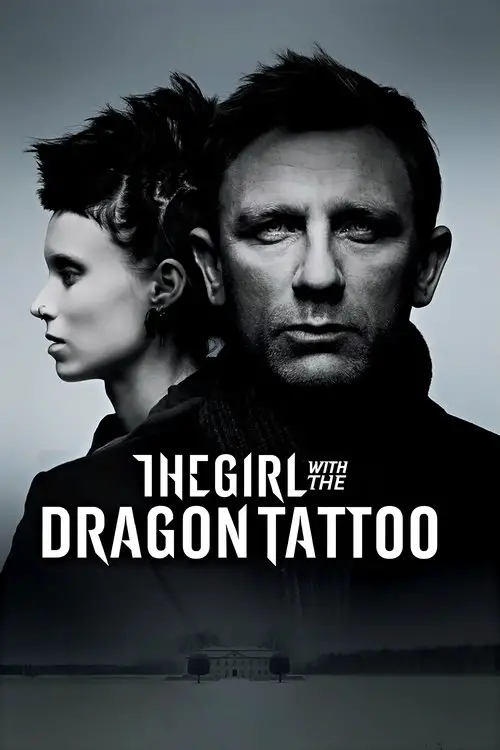
After taking a bullet to the head, Salander is under close supervision in a hospital and is set to face trial for attempted murder on her eventual release. With the help of journalist Mikael Blomkvist and his researchers at Millennium magazine, Salander must prove her innocence. In doing this she plays against powerful enemies and her own past.
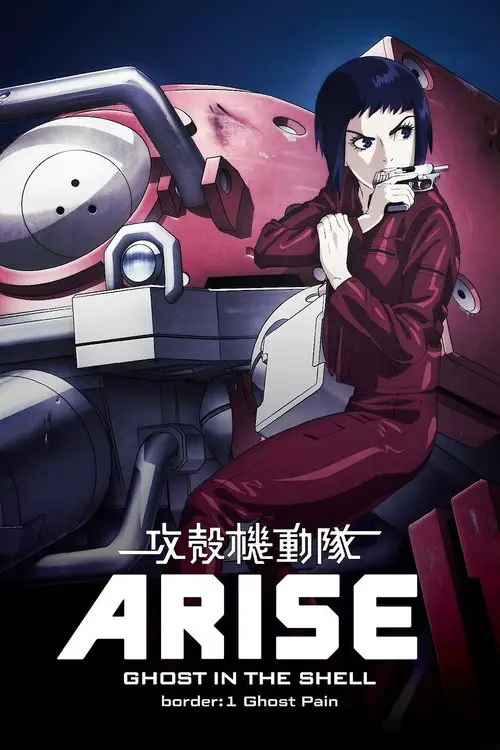
The story takes place in the year 2034, two years after the events in Ghost in the Shell: S.A.C. 2nd GIG. Female cyborg Major Motoko Kusanagi has left Public Security Section 9, an elite counter-terrorist and anti-crime unit specializing in cyber-warfare, which has expanded to a team of 20 field operatives with Togusa acting as the field lead.
This English-language adaptation of the Swedish novel by Stieg Larsson follows a disgraced journalist, Mikael Blomkvist, as he investigates the disappearance of a weary patriarch's niece from 40 years ago. He is aided by the pierced, tattooed, punk computer hacker named Lisbeth Salander. As they work together in the investigation, Blomkvist and Salander uncover immense corruption beyond anything they have ever imagined.
Nick is excited to discover that he's won a dinner date with his favorite actress, Jill Goddard. But when Jill refuses to honor the contest, he receives an offer he can't refuse: the ability to view Jill secretly via computer. Nick begins watching the unknowing star on her webcam, not realizing that this decision will put both himself and Jill at risk as they enter a terrifying world of cat-and-mouse where nothing-and no one-are as they seem.
Ji-hyuk is an expert safe-cracker who lives the highlife stealing antiques and jewelry with his team. CHO, a powerful and cruel gang boss threatens them to steal $150 million with him. Ji-hyuk plans to get revenge on CHO, but ends up falling into his trap. However, CHO later realizes it was all part of Ji-hyukâs scheme. When Ji-hyuk, who was thought dead, reappears, hidden secret relations between the technicians also surface.
Bill Pope is a CIA agent on a mission in London tracking down a shadowy hacker nicknamed "The Dutchman." When he gets mysteriously ambushed and killed, an experimental procedure is used to transfer his memories into dangerous ex-convict Jericho Stewart. When he wakes up with the CIA agent's memories, his mission is to find The Dutchman and eliminate him before the hacker launches ICBM's and starts World War III. But complications soon arise and the mission turns personal.
political thriller that charts the exploits of disillusioned ex-hacker Terell Lessor. A return to New York, coupled with a humiliating attempt at getting a new job, serves as the catalyst for him to take action against those who slighted him in the past. Employing strategically placed spy-cams, and operating in tandem with backer, strategist and lover Olivia, he captures compromising footage and broadcasts the edited clips via a newly-minted website. Recognizing the power of their model, the two begin to target CEOs, politicians, those who represent the worst of the establishment. Soon Terell's every move is front-page news, law enforcement is after him, and copy-catters are taking his abduction-and-confession model to extremes he never imagined. With these forces colliding, Terell has to decide whether his actions are sustainable - a decision that will compromise his agenda, his first taste of romance, and his physical wellbeing.
FAA system analyzer named Neil McCabe is the only person who seems to have this different hunch towards a group of international terrorists after a horrific plane incident occured. He thinks that an evil genius computer hacker sets out and manipulate the computer electronical system which linked to several airplanes to cause destruction and tragedy. In order to prevent the mishap, McCabe and his teammate, Rudy, finds out about the machine used by the criminals which leads them to a psychotic thrilling fight between the terrorist.
When a new airplane that's equipped with a new computer that can fly the plane on its own, is about to have its first flight. But the son of the owner decides to upload more software, he doesn't bother to check if there are any viruses with it. And he also invites some potential investors to try it. So the plane appears to be working well but suddenly it veers off course and it can't be shut down. When the military learns of this and fears what if something happens if it's over a populated area; decides to shoot it down along with everyone on board. The man who built the computer whose wife is among the passengers thinks if he can get on board he might be able to shut it down and regain control of the plane. So the military using a new plane gets him on board. But what he didn't know is that both pilots are incapacitated so there's no one who can fly the plane.
After a tragic accident Luke Gibson is left with critical injuries and complete amnesia. A new technological breakthrough from the Hexx Corporation - a Psi-Comp Implant that's hardwired into Luke's brain - saves his life, but Luke soon finds out that this new technology comes with a price and that the Hexx Corporation harbors sinister plans for the new device.
Kevin Mitnick is quite possibly the best hacker in the world. Hunting for more and more information, seeking more and more cyber-trophies every day, he constantly looks for bigger challenges. When he breaks into the computer of a security expert and an ex-hacker, he finds one - and much more than that...
Hackers Wanted is an unreleased American documentary film. Directed and written by Sam Bozzo, the film explores the origins and nature of hackers and hacking by following the adventures of Adrian Lamo, and contrasting his story with that of controversial figures throughout history. The film is narrated by Kevin Spacey.
Notorious hacker Drew Reynolds is captured by the CIA and given a proposition - work for them or spend the rest of his life in prison. Agreeing on the condition that he can form his own team, he puts together a group of "throwaways" - the people deemed expendable and seemingly the worst in the organization.
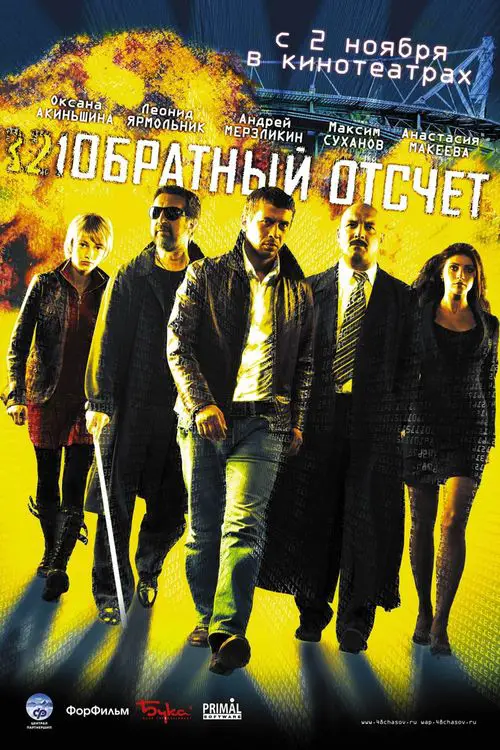
There will be an explosion exactly in 48 hours in Moscow. The information was provided by an agent who was killed this very second. All departments of special ops work on it, but the only hope is for recently organized independent team. They are a hacker girl who once broke thru Pentagon servers, a former special ops officer who enjoys speed and adrenalin, psychologist, a lady whose beauty outshines her intelligence and her rank of major, and a blind field engineer whose sense of smell and intuition substitute for his eye sight... And the Chief who got them all together and learned how to control them. Only this team is able to figure it out WHO, and most importantly WHERE, by knowing just WHEN...
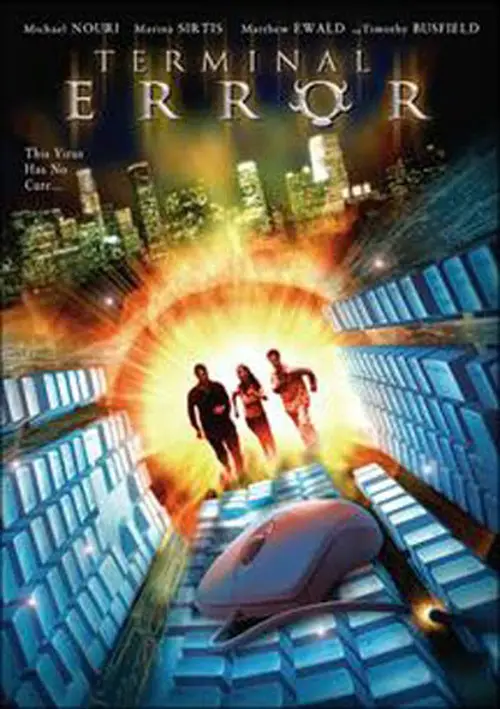
Michael Nouri stars in this high-tech thriller as Brad Weston, a digital tycoon who must fend off attacks from his former partner, who's unleashed a computer virus onto the entire system at his firm Autocom. But the virus appears to be a true menace that's determined to destroy anyone -- or anything -- that comes its way. Now, Weston must rely on his son (Matthew Ewald), a teenager with a penchant for hacking, to stop the menace in its tracks.
It's been 10 years since John Connor saved Earth from Judgment Day, and he's now living under the radar, steering clear of using anything Skynet can trace. That is, until he encounters T-X, a robotic assassin ordered to finish what T-1000 started. Good thing Connor's former nemesis, the Terminator, is back to aid the now-adult Connor ⦠just like he promised.
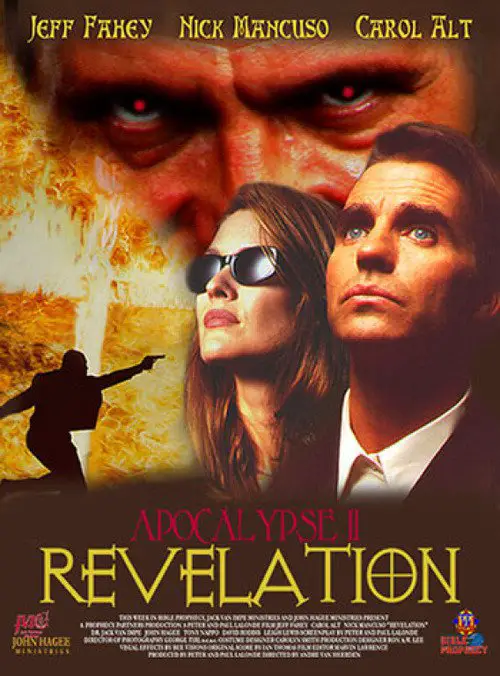
This is the sequel to Apocalypse. In this movie Thorold Stone is still looking for his family. The Christians, whom the rest of the world has started to call The Haters, are being framed for many murders and terrorist acts. Thorold and his partner go to investigate the location of the detonator of one of these acts. They find a group of Christians holding a service. He arrests them and one of them hands him a disk from O.N.E. , One Nation Earth. He finds men in the building who aren't Christians. They chase them around and one of them is killed. Then he meets with Mr. Parker who works for Franco Malacousso. Parker shoots them both but Thorold doesn't die. He is then framed for the shooting of his partner and he goes to a computer programmer with the disk. Virtual Reality is used to bring the Day of Wonders to fruition. There is something odd about the cd that the woman gave Thorold because the programmer can't get access to it and they take it to the Christians headquarters...
Bill Marks is a burned-out veteran of the Air Marshals service. He views the assignment not as a life-saving duty, but as a desk job in the sky. However, today's flight will be no routine trip. Shortly into the transatlantic journey from New York to London, he receives a series of mysterious text messages ordering him to have the government transfer $150 million into a secret account, or a passenger will die every 20 minutes.
Six months after the events depicted in The Matrix, Neo has proved to be a good omen for the free humans, as more and more humans are being freed from the matrix and brought to Zion, the one and only stronghold of the Resistance. Neo himself has discovered his superpowers including super speed, ability to see the codes of the things inside the matrix and a certain degree of pre-cognition. But a nasty piece of news hits the human resistance: 250,000 machine sentinels are digging to Zion and would reach them in 72 hours. As Zion prepares for the ultimate war, Neo, Morpheus and Trinity are advised by the Oracle to find the Keymaker who would help them reach the Source. Meanwhile Neo's recurrent dreams depicting Trinity's death have got him worried and as if it was not enough, Agent Smith has somehow escaped deletion, has become more powerful than before and has fixed Neo as his next target.
Hacker's Game is a love story between two hackers, Soyan and Loise. Like many other hackers, Soyan works for a company he previously hacked. This "online security" firm runs covert activities for high-profile clients around the world. Loise is a cyber-detective who investigates war crimes for a human rights organization. Obsessed with the truth, she also has spent years searching for an unknown person. The two hackers meet on a rooftop and bond together through a virtual chess game. But Soyan's employer, Russell Belial, has asked him to protect the same arms-dealer that Loise is determined to help to capture. Who will call the game now? What is Soyan's real goal? The pair embarks upon an intense but dangerous romance, playing an elaborate game of deception. After being in a virtual world, will Soyan and Loise risk everything for true love?
The movie's plot is based on the true story of a group of young computer hackers from Hannover, Germany. In the late 1980s the orphaned Karl Koch invests his heritage in a flat and a home computer. At first he dials up to bulletin boards to discuss conspiracy theories inspired by his favorite novel, R.A. Wilson's "Illuminatus", but soon he and his friend David start breaking into government and military computers. Pepe, one of Karl's rather criminal acquaintances senses that there is money in computer cracking - he travels to east Berlin and tries to contact the KGB.
Samuel works in Brussels as a pharmaceutical delivery man. His gorgeous girlfriend Mireille heads off to New York to intern at a prestigious architecture firm. Shortly after her departure, Sam's computer is hacked. A series of rather dodgy IT-guys fail to protect his wireless network. The mysterious hacker seems intent on screwing up Samuel's life and his relationship with Mireille. Paranoia kicks in. Sam starts to suspect his neighbors and gets obsessed with WiFi-rays... Love, paranoia and two lovers separated by an ocean of communication devices.
Emma is a young and beautiful graduate student just starting a new life in New York City. Like most people her age, she is always connected - her phone and laptop are constant companions, documenting her most intimate moments. What she doesn't realize is that she's sharing her life with an uninvited and dangerous guest. A hacker is following Emmaâs every move. When the voyeuristic thrill of watching her digitally isn't enough, the situation escalates to a dangerous and terrifying level.
Faced with her parents' recent divorce, her mother working long hours and her high school boyfriend dumping her, 16-year-old Martha looks for solace in the world of Internet chat rooms. Innocent chatting turns deadly as Martha attracts the attention of a pedophile and cyber-kidnapping ring. Martha's mother Connie suspects foul play and begins a frantic search for her daughter, enlisting the help of the police, the FBI and an expert hacker.
The story is set in 2027, one year after the end of the fourth non-nuclear war. New Port City is still reeling from the war's aftermath when it suffers a bombing caused by a self-propelled mine. Then, a military member implicated in arms-dealing bribes is gunned down. During the investigation, Public Security Section's Daisuke Aramaki encounters Motoko Kusanagi, the cyborg, wizard-level hacker assigned to the military's 501st Secret Unit. Batou, a man with the "eye that does not sleep," suspects that Kusanagi is the one behind the bombing. The Niihama Prefectural Police detective Togusa is pursuing his own dual cases of the shooting death and a prostitute's murder. Motoko herself is being watched by the 501st Secret Unit's head Kurutsu and cyborg agents.
Personal injury attorney Stuart Pepper faces the challenge of his young career when he takes on a controversial case of wrongful death in small town Iowa. Kevin Thacker's body was found in the alley outside the Marshalltown Police Department after the young man was arrested for drunk driving. The arresting officer's story is highly suspicious and everyone involved, from the investigating detective to the FBI, appear to be aiding in covering up what actually happened that fateful night. With a promise made to the Thacker family to expose the truth, Stu dives head first into an uphill battle against lies and corruption. What transpires will change this lawyer's life forever.
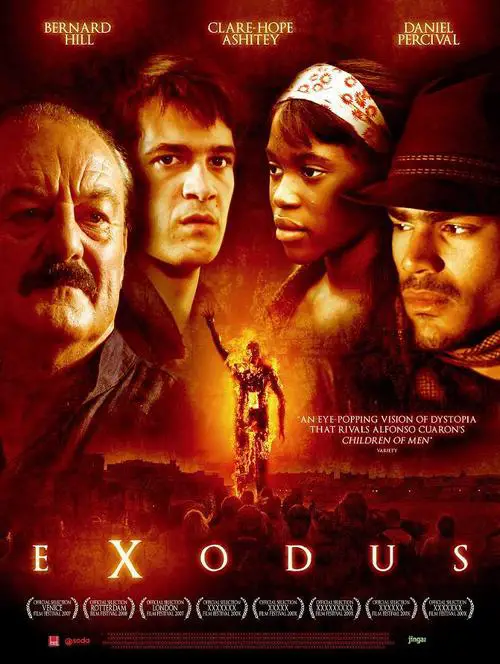
The story of Exodus is relocated to the seaside town Margate. Moses lives in the Promised Lands with his adoptive parents, until he finds his mother in the shanty town, Dreamland, where sheâs been ghettoised with other âundesirablesâ. He takes on his father, Pharaoh, and leads a radical campaign to liberate the people of Dreamland.
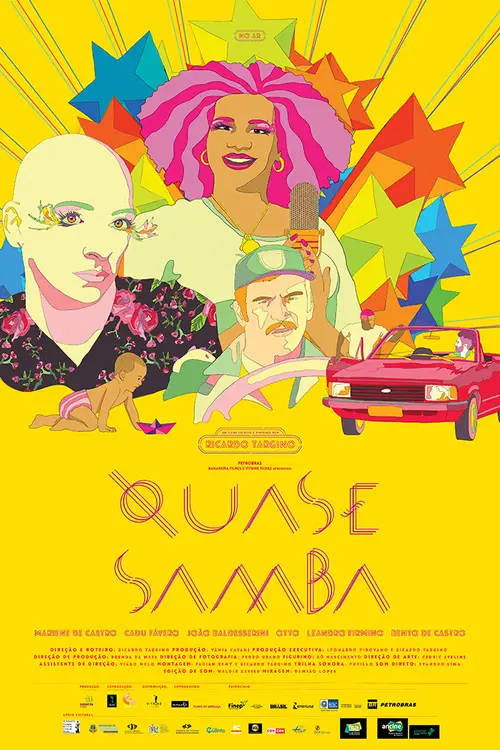
In the short end of pregnancy, a samba singer sees herself shared between two men that believes to be the father of her baby. Duelling men: a militiaman, a hacker and Shirley, a cross-dresser, best friend of the singer, who really plays the role of head on that family. Dreams, love, jealousy, life and death. Like in our songs.
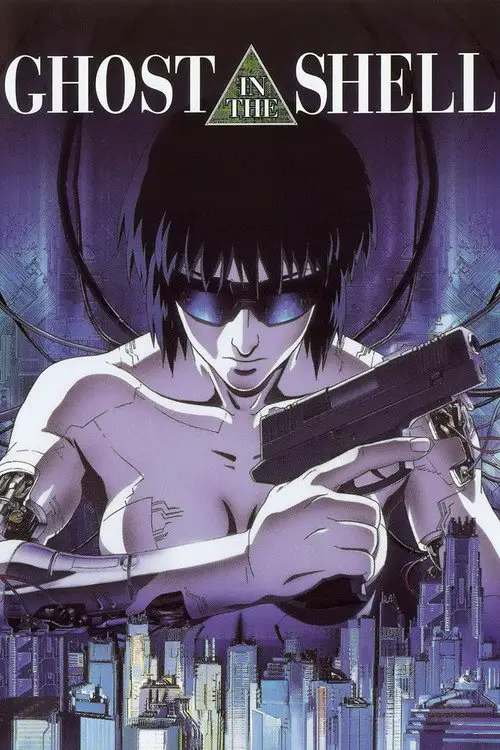
In the year 2029, the barriers of our world have been broken down by the net and by cybernetics, but this brings new vulnerability to humans in the form of brain-hacking. When a highly-wanted hacker known as 'The Puppetmaster' begins involving them in politics, Section 9, a group of cybernetically enhanced cops, are called in to investigate and stop the Puppetmaster.
In a futuristic world, Michelle lives everyday battling with DNA Hackers who use their skills to hack into people's bodies and kill them. She is an assassin, trying to keep her younger brother, Jackie, out of trouble. When Jackie gets involved in a petty crime of robbery, he propels himself into the world of DNA Hackers, Shylocks (Loan Sharks) and Gangs
A.D. 2400, DEVA's central council detects an incident of unauthorized access into their mainframe. Someone on Earth was trying to hack into the system. The only information DEVA was able to retrieve was that hacker referred to themselves as "Frontier Setter." To investigate the mysterious hacker's motives, the high officials of DEVA dispatch system Security Third Officer Angela Balzac to the Earth's surface. Equipped with a prosthetic "material body," Angela attempts to make contact with a local agent Dingo, but what awaited her instead was a swarm of Sandworms now infesting the Earth's surface. Angela intercepts the gruesome pests with her exoskeleton powered suit Arhan.
© Valossa 2015–2026
| Privacy Policy